Dangers in the Modern Era of Business Information Technology
Introduction
The broad accessibility of powerful technological tools in today's business world enables enormous value not seen even ten years ago. With little capital investment or technological training, businesses can deploy file storage, structured databases, analytical tools, communications systems of all kinds, payment systems, accounting and project management systems, customer relations applications, websites, virtual servers, and software development platforms.
This era of convenience and simplicity brings with it a new range of dangers to your information security. To see the extent of this, let's review what defines the current era and the new threats it brings. We'll then discuss how best to protect your company's information security assets.
The Current Era
These aspects of information technology define the modern era and enable the broad accessibility described above:
- A market where consumer electronics are almost entirely merged with business equipment and applications for small business.
- User-based rather than system- or network-based applications.
- The vast availability of free or inexpensive applications accessible over the Internet via a web browser or mobile device app.

The merging of consumer and business technology is defined mostly by increased mobility and ubiquity. The earliest pocket computers and smart phones were mainly for business use (organizer, corporate e-mail, documents and spreadsheets), and only executives or other sophisticated employees had one. Mobile devices now cost much less, relatively, given their capabilities; almost everyone has one; and they can run almost any application, whether for navigation, dating, games, movies, music, messaging, social media, hobbies, or business. Cellular data is unlimited with many plans. As a result, almost every small business encourages employees to use their privately owned phones or tablets to access company resources directly through their own Internet access accounts, saving the company from having to purchase and maintain mobile devices and data plans. We used to have a term for this—Bring Your Own Device (BYOD)—but we hardly see this term anymore since it's now the norm, and not something we need to label.
System- or network-based applications were (and still are) installed by IT system administrators on a user's workstation, or by the user himself in permissive environments. Then, the software must be configured to access shared information, such as a database on the company server or a shared folder, which might require additional networking software to make the connection when away from the office. If the system requires login, the administrator must create the account and assign the access level. In the modern era, accessing an application is as easy as a user typing his e-mail address and desired password to register an account, and the services immediately become available for use. Users find each other and share information as they choose, with little control, if any, by a system administrator.

Finally, there is an enormous amount of applications available, almost all with a free offering, that can be accessed on any kind of computer or modern mobile device. Users find these on their own, sign up, and invite their co-workers. They can build websites and databases, share files, and generate reports all without involvement of the IT department. Compatibility is not an issue, because all modern applications run in a standard web browser found on every computer or mobile device.
The Dangers
The perils of the modern era fall into four general categories.
- A rogue employee stealing information (the insider threat)
- Losing management visibility and control of data
- Hardware or software failure leading to data loss or corruption
- Criminals infiltrating your systems to steal or corrupt data, possibly for ransom
None of these are new. They are, however, amplified in the era of easy access.
Rogue Employees

Employees could steal information before we had computers, by taking papers out of the file cabinet. In prior eras of business computing, they could e-mail a limited number of files to themselves, or burn a few hundred megabytes to a CD. But with plenty of online storage now available for free or inexpensively (through Dropbox, Box, Google Drive, Microsoft OneDrive, and Apple iCloud), and much faster Internet connections, it's now easy for users to copy large amounts of company information to their own personal storage. And they can do this from home after-hours, making it harder to detect.
Management Visibility and Control
Even if your employees have no ill intentions, unless the distribution of your information is properly controlled (through policy, training, and technical measures), you could lose access to it anyway. This happens if you don't have a system for designating where data goes, and ensuring users put the data where it belongs.
This is more of a problem today than in the recent past. Learn more about the potential impact in this article on the J.D. Fox Exec website entitled Taking Control of Your Data (opens in a new tab).
System Failures
Cloud services go offline every so often. Usually, the provider gets their systems back online soon enough. In rare occasions, they can go offline permanently.
In the past era, with on-premises equipment hosting your applications and data, it was all on your IT staff to fix outages. However, you had full control of your systems. With detailed knowledge of the situation and expected time to restore service, you could keep users informed and alter your operations to work around the outage in the most optimal fashion. In addition, with back-end access to your system configuration information and operational databases and files, your IT manager could set up redundancy systems and make backups for faster recovery and more robust protection.
The challenges of managing outages are amplified in the modern era in a few ways:
- When cloud services go down, there is little you can do but wait until it's fixed, and you may have no way to know whether it's going to be hours or days. For some cloud applications, you can set up redundancy to enable business operations to continue in the event of an outage, but for many it's not possible, or at the very least it's as complicated and expensive as with on-premises systems.
- If data is lost, it may be lost forever if you have no backup. Not all cloud systems are amenable to the kind of granular and robust backup you can have with on-premises equipment. For example, if a user wipes out some records in a database, or a database administrator accidentally fills the ZIP Code column in the entire customer list with "12345" while testing some database update functions, your IT manager could recover from this with direct access to the database transaction logs if your database is stored on your own equipment. But in a cloud database system, depending on the provider, recovery may not be possible.

To read more, including details on data backup in the cloud, see this article entitled Cloud Providers and the Safety of Your Data (opens in a new tab).
Infiltration
Computer viruses have been around for decades, and scams inducing people to give up their passwords just as long. In the modern era, these threats are accelerated in two ways:
- Company controlled devices can be locked down with endpoint security software (formerly called anti-virus) to prevent the computer from being infected with malware. When users own or control their devices, these systems can be uninstalled or easily bypassed.
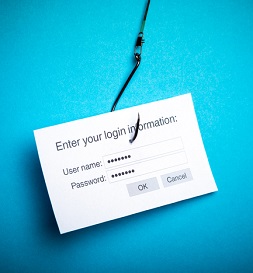
- Users are prompted to log in for just about everything they do on a workstation or mobile device these days. And, with many separate login accounts, they may be inclined to use the same password for all or most of them. Given this, password stealing has a greater chance of success and will cause greater damage. People often receive fraudulent but realistic-looking messages with a web link claiming there's an online document to read. The linked site presents a fake prompt for the user to log in with his Microsoft or Google account. If the user enters his e-mail address and password, the site captures that information, and the user's account is now compromised. A stolen password causes more damage in the modern era because of the great amount of files users typically have accessible through their cloud account, and because the criminal will try the same e-mail address and password in other common cloud services, with a good chance of success.
Apart from devices and user accounts, your cloud service providers themselves are likely under attack to a much greater extent than your on-premises systems were. Opportunistic criminals try to get into the popular platforms to see what they can find. They're looking for a leaked password list or a flaw in the cloud provider's servers that can get them in without a password. So when there's a breach, they get into the cloud system itself, and potentially all of its customers' data is then exposed. When you had your own systems on premises, criminals would try to connect as well, but a successful attack on a large company wouldn't mean your systems were then compromised.
Solutions

To address these issues properly, you need a three-pronged approach:
- Secure devices. This involves endpoint security software to protect against malware, and mobile device management (MDM) systems to enforce policies. Such policies would enable a level of control over devices, even those owned by the employee, and prevent any unknown devices from connecting.
- Monitor and control cloud access. This can include data-loss prevention (DLP) systems supported by your cloud applications, or more sophisticated cloud access security broker (CASB) systems, both of which would rely on your MDM. For your more complex assets, such as software development or application-hosting platforms, this includes application firewalls, and intrusion detection or intrusion prevention systems.
- Implement robust identity management and access control. This enables single sign-in (SSO), the capability to create one login account for your users to access all cloud services, instead of a separate account for each application. This would include employees, customers, and partners, all under one system. It would also enable use of two-factor authentication (through the user's personal cell phone, for example), but allow the company to take control of the account in the event of a user's sudden departure. The access control aspect involves standard permissions management and classification of data, but can also include sophisticated systems such as context-aware access control, where a user is blocked when the mode of access is incorrect, or it appears the login account may have been breached. An example of incorrect mode of access might be where a salesman tries to download the entire customer list from your sales management application using a database management tool, instead of using the normal web-based interface for salespeople to view information on one customer at a time. A potential breach might be identified if a user logs in from Los Angeles, and moments later logs in from Moscow.
Technological solutions for all of these exist, as described in this article on the J.D. Fox Exec website entitled Tools and Technologies Available for Information Security (opens in a new tab).
By themselves, however, these represent point solutions only, which is a term describing an application or system that addresses one particular aspect of a problem. That is, if you contact the publishers or reseller partners of these technological security solutions for pricing, evaluate the products for their capabilities and cost, make the purchase, and deploy, you will not end up with a comprehensive security solution, even if you have all three prongs covered.

For successful implementation of an information security program, you must incorporate physical and administrative controls, such as a policy for managing laptop and tablet hardware, involving HR in on-boarding and training, monitoring and controlling the performance of your technological security tools, etc. Training and information security awareness are also key components to success.
The effects of this integration of IT security with operations—a cornerstone of an information security program—are many. Some examples:
- Efficient and effective user account management. Creating a new employee's single sign-in account can be handled by HR during on-boarding. On departure, the HR manager could shut down the account without involvement of IT, immediately securing all company assets the user could access.
- Different components of IT security support each other. Context-aware access control doesn't work without a good identity management system, and you cannot fully secure users' access to the cloud without control of the devices they use.
- A culture of information security. When employees and customers see how access control and proper permissions are considered in everything the company does, without impacting productivity, then the lax and open access they might have seen in other companies will appear distateful. This will inspire confidence in the quality of your company's governance. And with good training, users will learn how to be vigilant against threats, particularly targeted threats from malicious actors.
- Visibility and control over the entire information landscape. Any information assets—files, databases, virtual machines, and application platforms—can be inventoried, located, secured with proper permissions, removed from any user or department and assigned to another, and duplicated for resilience and disaster recovery. This maximizes assurance of confidentiality, integrity, and availability of your data.
Epilogue
If you've been in business many years and haven't adjusted your management approach for the modern era, or if you're a younger manager who has built your department or company on BYOD and cloud services without considering information security, you may be subjecting your assets to unnecessary risk. Reducing these risks is best managed by establishing an Information Security program.
To get started, visit J.D. Fox Exec today.